In the ever-shifting landscape of cybersecurity, organizations ought to constantly adjust their defenses to combat novel cyber threats. A robust security framework includes multiple layers of protection, from intrusion detection systems to robust authentication. Regular security audits and red team exercises are essential for identifying weaknesses
 Anthony Michael Hall Then & Now!
Anthony Michael Hall Then & Now!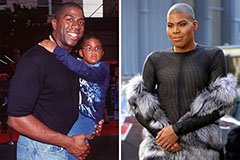 Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Karyn Parsons Then & Now!
Karyn Parsons Then & Now! Nancy Kerrigan Then & Now!
Nancy Kerrigan Then & Now! Jane Carrey Then & Now!
Jane Carrey Then & Now!